MIC
Defense
Technological sovereignty, security, and auditability.
In defense, institutional control and technological sovereignty are strategic priorities. Digitalization must reinforce security and auditability.
Industry challenges
Protect critical knowledge and control access.
Technical information must be compartmentalized and traceable.
Exhaustive traceability for strategic programs.
Each component must be verifiable with a complete evidence chain.
Compliance with specific security requirements.
Architecture must align with segregated networks and controlled deployment.
Operational continuity in protected environments.
Operations must remain stable under connectivity restrictions.
MIC Solution
In defense, MIC protects critical knowledge and ensures full auditability. The architecture meets sovereignty requirements.
MIC Repositorio Digital
Implements granular access control and secure management of sensitive documentation. Critical information remains compartmentalized and traceable.
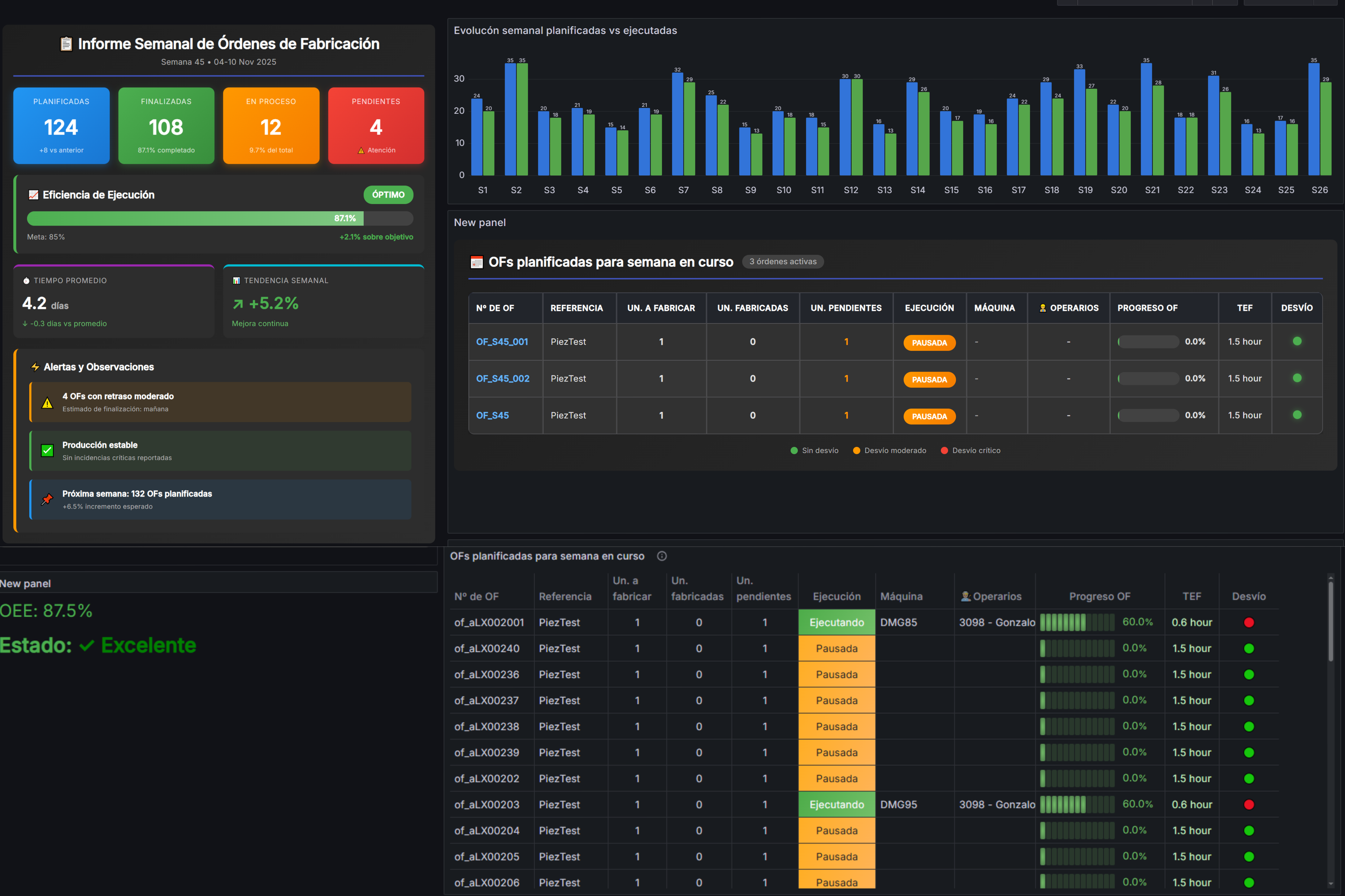
View solutionMIC Operation System
Ensures verifiable traceability of every operation performed. Strengthens the evidence chain in strategic programs.
View solutionMIC Monitoring
Monitors assets in real time within protected environments. Maintains operational visibility under security constraints.
View solutionDeployable architecture in local or hybrid environments maintains data sovereignty and operational continuity.
Typical architecture
Secure deployment in a protected network → Controlled repository → MIC Operation System → Segregated MIC Monitoring → Institutional ERP integration.
